česky | english
TLS/SSL Scanner
Contents
The following sections present tools and sites for scanning or testing servers or clients for their respective TLS/SSL capabilities.
1. DCSec
The DCSEC research group at Leibniz University Hannover, Germany, provides a service that
- "...gives you information on the SSL cipher suites your browser supports for securing HTTPS connections."
Surf to https://cc.dcsec.uni-hannover.de with the browser to be examined.
2. GnuTLS
Install the GnuTLS command line utilities and run these commands in a terminal:
$ gnutls-cli --insecure --port 443 --print-cert --verbose HOSTNAME $ gnutls-cli-debug --port 443 --verbose HOSTNAME
See the documentation for further details.
3. Nmap Security Scanner
Use the Nmap Security Scanner with the ssl-enum-ciphers script at the command line
$ nmap --script ssl-enum-ciphers -p 443 HOSTNAME
to scan a server.
- "This script repeatedly initiates SSL/TLS connections, each time trying a new cipher or compressor while recording whether a host accepts or rejects it. The end result is a list of all the ciphers and compressors that a server accepts."
Please note:
Running this script is intrusive since it must initiate many connections to a server, and therefore is quite noisy. It takes several minutes.
For further details see the Nmap documentation and the script's source.
3.1. Example: secure.cacert.org
The following example examines the host secure.cacert.org:
1 $ nmap --script ssl-enum-ciphers -p 443 secure.cacert.org
2 Starting Nmap 6.00 ( http://nmap.org ) at 2014-10-21 21:06 CEST
3 Nmap scan report for secure.cacert.org (213.154.225.246)
4 Host is up (0.072s latency).
5 PORT STATE SERVICE
6 443/tcp open https
7 | ssl-enum-ciphers:
8 | TLSv1.0
9 | Ciphers (12)
10 | TLS_DHE_RSA_WITH_AES_128_CBC_SHA - strong
11 | TLS_DHE_RSA_WITH_AES_256_CBC_SHA - unknown strength
12 | TLS_DHE_RSA_WITH_CAMELLIA_128_CBC_SHA - unknown strength
13 | TLS_DHE_RSA_WITH_CAMELLIA_256_CBC_SHA - unknown strength
14 | TLS_DHE_RSA_WITH_SEED_CBC_SHA - unknown strength
15 | TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA - strong
16 | TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA - unknown strength
17 | TLS_RSA_WITH_AES_128_CBC_SHA - strong
18 | TLS_RSA_WITH_AES_256_CBC_SHA - unknown strength
19 | TLS_RSA_WITH_CAMELLIA_128_CBC_SHA - unknown strength
20 | TLS_RSA_WITH_CAMELLIA_256_CBC_SHA - unknown strength
21 | TLS_RSA_WITH_SEED_CBC_SHA - unknown strength
22 | Compressors (1)
23 | NULL
24 | TLSv1.1
25 | Ciphers (12)
26 | TLS_DHE_RSA_WITH_AES_128_CBC_SHA - strong
27 | TLS_DHE_RSA_WITH_AES_256_CBC_SHA - unknown strength
28 | TLS_DHE_RSA_WITH_CAMELLIA_128_CBC_SHA - unknown strength
29 | TLS_DHE_RSA_WITH_CAMELLIA_256_CBC_SHA - unknown strength
30 | TLS_DHE_RSA_WITH_SEED_CBC_SHA - unknown strength
31 | TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA - strong
32 | TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA - unknown strength
33 | TLS_RSA_WITH_AES_128_CBC_SHA - strong
34 | TLS_RSA_WITH_AES_256_CBC_SHA - unknown strength
35 | TLS_RSA_WITH_CAMELLIA_128_CBC_SHA - unknown strength
36 | TLS_RSA_WITH_CAMELLIA_256_CBC_SHA - unknown strength
37 | TLS_RSA_WITH_SEED_CBC_SHA - unknown strength
38 | Compressors (1)
39 | NULL
40 | TLSv1.2
41 | Ciphers (24)
42 | TLS_DHE_RSA_WITH_AES_128_CBC_SHA - strong
43 | TLS_DHE_RSA_WITH_AES_128_CBC_SHA256 - strong
44 | TLS_DHE_RSA_WITH_AES_128_GCM_SHA256 - strong
45 | TLS_DHE_RSA_WITH_AES_256_CBC_SHA - unknown strength
46 | TLS_DHE_RSA_WITH_AES_256_CBC_SHA256 - unknown strength
47 | TLS_DHE_RSA_WITH_AES_256_GCM_SHA384 - unknown strength
48 | TLS_DHE_RSA_WITH_CAMELLIA_128_CBC_SHA - unknown strength
49 | TLS_DHE_RSA_WITH_CAMELLIA_256_CBC_SHA - unknown strength
50 | TLS_DHE_RSA_WITH_SEED_CBC_SHA - unknown strength
51 | TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA - strong
52 | TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256 - strong
53 | TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 - strong
54 | TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA - unknown strength
55 | TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 - unknown strength
56 | TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 - unknown strength
57 | TLS_RSA_WITH_AES_128_CBC_SHA - strong
58 | TLS_RSA_WITH_AES_128_CBC_SHA256 - strong
59 | TLS_RSA_WITH_AES_128_GCM_SHA256 - strong
60 | TLS_RSA_WITH_AES_256_CBC_SHA - unknown strength
61 | TLS_RSA_WITH_AES_256_CBC_SHA256 - unknown strength
62 | TLS_RSA_WITH_AES_256_GCM_SHA384 - unknown strength
63 | TLS_RSA_WITH_CAMELLIA_128_CBC_SHA - unknown strength
64 | TLS_RSA_WITH_CAMELLIA_256_CBC_SHA - unknown strength
65 | TLS_RSA_WITH_SEED_CBC_SHA - unknown strength
66 | Compressors (1)
67 | NULL
68 |_ Least strength = unknown strength
69
70 Nmap done: 1 IP address (1 host up) scanned in 135.04 seconds
4. OpenSSL
Install the OpenSSL command line tools and run this command in a terminal:
$ openssl s_client -connect HOSTNAME:443 -prexit -showcerts -state -status -tlsextdebug -verify 10
Further details might be available in the OpenSSL documentation... ![]()
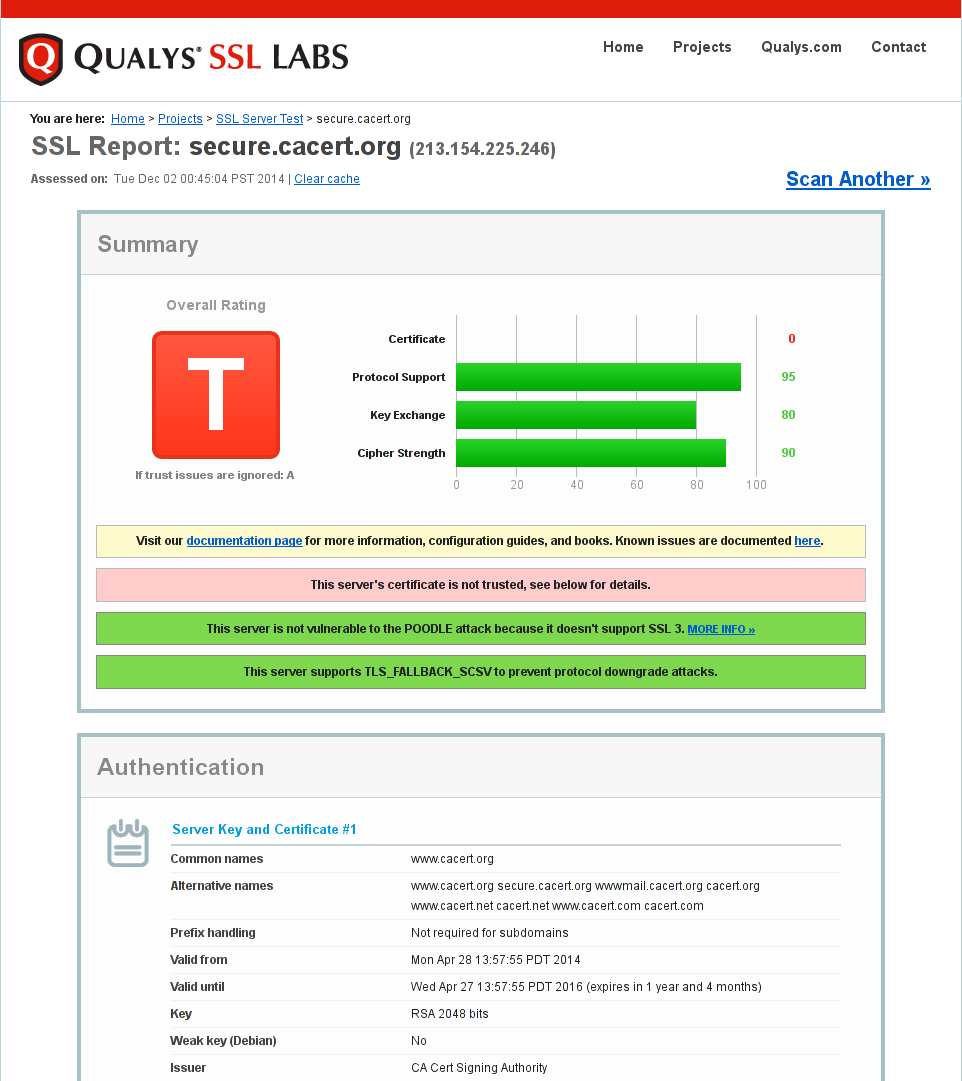
5. Qualys SSL Labs
Qualys SSL Labs provides two tests:
Use the very detailled SSL/TLS Server Test to scan a server. Note that this test uses the certificate store maintained by Mozilla.
See the SSL/TLS Capabilities of Your Browser.
5.1. Example: secure.cacert.org
6. High_Tech bridge
The Swiss tester HT Bridge rates the security of domains with web servers, similarly to the preceding Qualys tester. You enter a domain only to performing the test. The tester displays a results report on the same web page after the test is finished.
![]() Attention! This tester doesn't work with IPv6 addresses yet (12.2015)
Attention! This tester doesn't work with IPv6 addresses yet (12.2015) ![]()
6.1. An example: testing the cacert.org domain
7. sslscan
A wrapper over OpenSSL to list the ciphers usable on a TLS/SSL server.
Please note:
The original project on http://sourceforge.net/projects/sslscan seems to be abandoned. A fork receiving more attention can be found on https://github.com/DinoTools/sslscan.
7.1. Example: www.cacert.org
The following example examines the host www.cacert.org:
1 $ sslscan --no-failed www.cacert.org
2
3 ___ ___| |___ ___ __ _ _ __
4 / __/ __| / __|/ __/ _` | '_ \
5 \__ \__ \ \__ \ (_| (_| | | | |
6 |___/___/_|___/\___\__,_|_| |_|
7
8 Version 1.8.2
9 http://www.titania.co.uk
10 Copyright Ian Ventura-Whiting 2009
11
12 Testing SSL server www.cacert.org on port 443
13
14 Supported Server Cipher(s):
15 Accepted TLSv1 256 bits ECDHE-RSA-AES256-SHA
16 Accepted TLSv1 256 bits DHE-RSA-AES256-SHA
17 Accepted TLSv1 256 bits DHE-RSA-CAMELLIA256-SHA
18 Accepted TLSv1 256 bits AES256-SHA
19 Accepted TLSv1 256 bits CAMELLIA256-SHA
20 Accepted TLSv1 128 bits ECDHE-RSA-AES128-SHA
21 Accepted TLSv1 128 bits DHE-RSA-AES128-SHA
22 Accepted TLSv1 128 bits DHE-RSA-SEED-SHA
23 Accepted TLSv1 128 bits DHE-RSA-CAMELLIA128-SHA
24 Accepted TLSv1 128 bits AES128-SHA
25 Accepted TLSv1 128 bits SEED-SHA
26 Accepted TLSv1 128 bits CAMELLIA128-SHA
27
28 Prefered Server Cipher(s):
29 TLSv1 256 bits ECDHE-RSA-AES256-SHA
30
31 SSL Certificate:
32 Version: 2
33 Serial Number: 979116
34 Signature Algorithm: sha512WithRSAEncryption
35 Issuer: /O=Root CA/OU=http://www.cacert.org/CN=CA Cert Signing Authority/emailAddress=support@cacert.org
36 Not valid before: Apr 28 20:57:55 2014 GMT
37 Not valid after: Apr 27 20:57:55 2016 GMT
38 Subject: /C=AU/ST=NSW/L=Sydney/O=CAcert Inc./CN=www.cacert.org
39 Public Key Algorithm: rsaEncryption
40 RSA Public Key: (2048 bit)
41 Public-Key: (2048 bit)
42 Modulus:
43 00:c4:83:f3:42:d0:0b:ee:f9:3f:e2:1f:63:c5:a3:
44 84:e3:fd:c5:c2:a7:68:16:62:da:88:58:45:a5:dd:
45 41:16:c0:e7:9e:3b:2e:13:36:ee:b4:83:12:ca:a8:
46 a6:a6:8d:6c:d6:e8:6e:67:f7:f3:90:bd:69:98:93:
47 ee:14:2b:6f:2a:a4:b2:f6:6a:8f:e7:4c:9f:f5:f5:
48 8b:97:18:fc:3c:91:a4:6d:69:d2:b3:8b:e8:6a:e1:
49 0f:db:b1:90:b2:19:16:21:a6:ec:db:25:bf:23:c5:
50 6b:26:86:20:48:7b:c9:78:38:d3:dd:e4:eb:d5:a9:
51 a5:0b:32:53:66:af:bd:8b:ac:f1:fb:fc:f4:f6:67:
52 b9:a2:d3:fe:61:6d:eb:f3:f2:7d:55:92:d1:74:ea:
53 ab:82:4e:78:52:71:8e:e0:46:14:a5:1d:cc:89:52:
54 52:35:5a:0b:b1:16:8d:50:06:3c:07:c7:a1:d5:79:
55 91:51:8c:05:dd:25:c5:06:49:82:11:e2:61:fa:f1:
56 af:5b:34:e8:cb:4d:cf:2d:ba:e7:35:c0:de:f3:27:
57 e4:ef:a5:d4:20:3d:9e:37:cd:48:09:2c:29:23:9b:
58 bd:d7:aa:27:18:73:6c:b8:b7:54:98:72:f4:16:0c:
59 9a:95:26:90:4e:6e:9c:9b:54:75:ca:2b:79:12:05:
60 c1:cb
61 Exponent: 65537 (0x10001)
62 X509v3 Extensions:
63 X509v3 Basic Constraints: critical
64 CA:FALSE
65 X509v3 Key Usage: critical
66 Digital Signature, Key Encipherment, Key Agreement
67 X509v3 Extended Key Usage:
68 TLS Web Client Authentication, TLS Web Server Authentication, Netscape Server Gated Crypto, Microsoft Server Gated Crypto
69 Authority Information Access:
70 OCSP - URI:http://ocsp.cacert.org/
71
72 X509v3 CRL Distribution Points:
73
74 Full Name:
75 URI:http://crl.cacert.org/revoke.crl
76
77 X509v3 Subject Alternative Name:
78 DNS:www.cacert.org, othername:<unsupported>, DNS:secure.cacert.org, othername:<unsupported>, DNS:wwwmail.cacert.org, othername:<unsupported>, DNS:cacert.org, othername:<unsupported>, DNS:www.cacert.net, othername:<unsupported>, DNS:cacert.net, othername:<unsupported>, DNS:www.cacert.com, othername:<unsupported>, DNS:cacert.com, othername:<unsupported>
79 Verify Certificate:
80 unable to get local issuer certificate
8. tlsfun
There are some test on tlsfun.de created by Hanno Böck.
9. ZMap
University of Michigan scientists developed ZMap, an open-source network scanner that easily can perform Internet-wide network studies.
https://zmap.io/sslv3 - POODLE Attack and SSLv3 Deployment